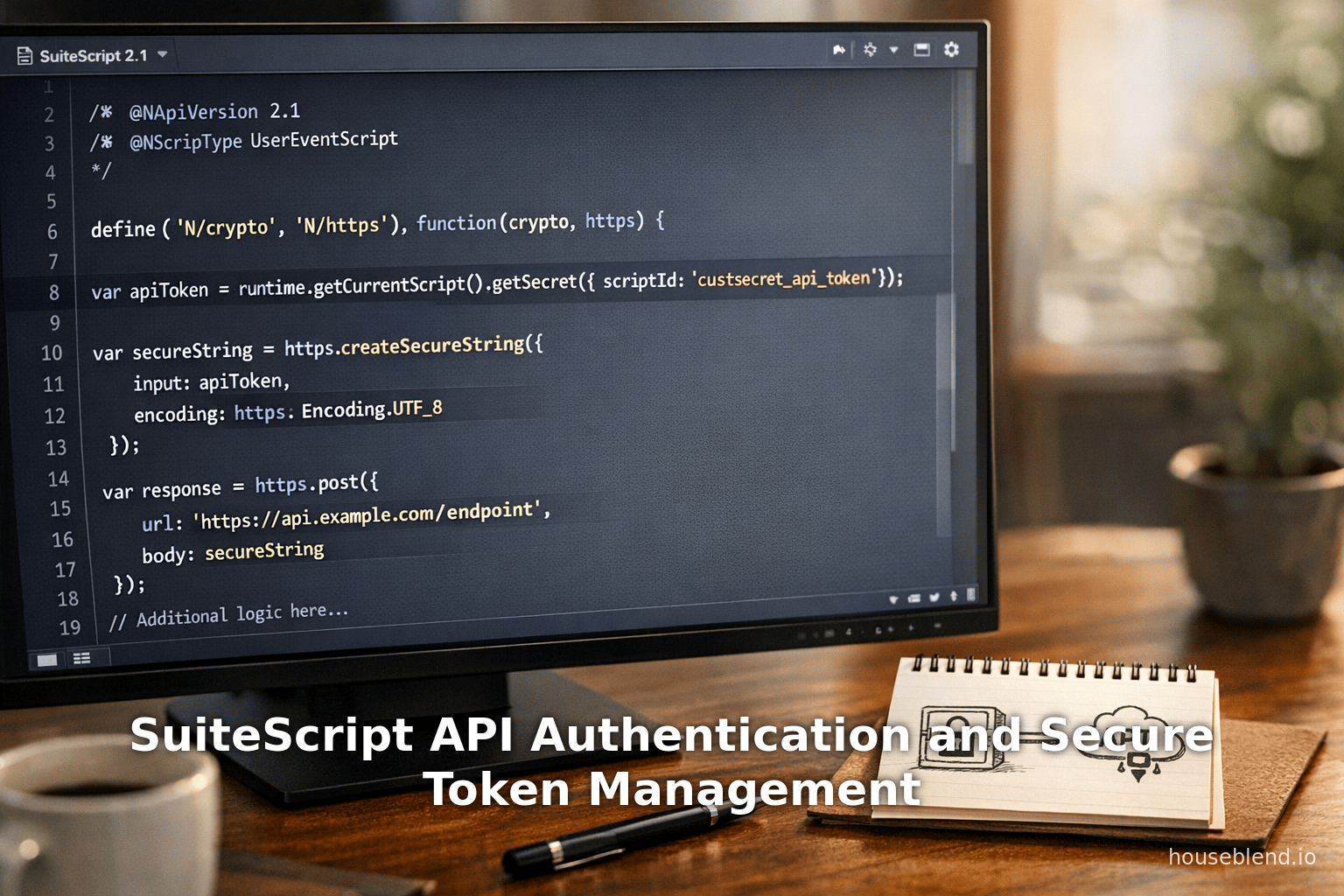
SuiteScript API Authentication and Secure Token Management
Executive Summary
NetSuite’s SuiteScript platform provides a rich set of modules and features to enable secure API authentication and token management. This report thoroughly examines the evolution, current state, and future of SuiteScript’s “credential module” capabilities. Key mechanisms include Form.addCredentialField (to capture sensitive data securely in Suitelets), the SuiteScript SecureString and SecretKey objects (via N/https and N/crypto modules), and NetSuite’s API Secrets feature (secure storage of encryption keys, tokens, and passwords). Together these tools allow developers to avoid hard-coding credentials, meet compliance requirements (e.g. PCI, GDPR), and mitigate rampant API-based security threats (e.g. breaches caused by exposed keys [1] [2]).
This report begins with background on SuiteScript and the imperative for security in cloud ERP integrations. We detail the timeline of enhancements – from early SuiteScript 2.x features (e.g. ServerWidget.addCredentialField in 2015.2 [3]) to the introduction of API Secrets (SuiteScript 2021.1) and the various N/https and N/crypto methods for encryption and secure strings [4] [5]. We analyze authenticaton patterns (Basic Auth, OAuth, JWT, client-cert) and how SuiteScript supports them (e.g. using https.createSecureString for headers [6], crypto.createHmac for signing [7]). We discuss best practices (domain restrictions, script ACLs, rotation, least privilege) and pitfalls (hard-coded secrets, improper logging, leaked keys). Extensive examples from Oracle documentation and NetSuite community blogs illustrate implementation.
We also survey real-world use cases and case studies: e-commerce integrations, payment gateways, and third-party data sync scenarios. Statistical data underscores the stakes – for example, 99% of organizations report API security issues and 95% of API attacks exploit valid credentials [1]. We conclude by projecting future directions (e.g. mutual TLS support via N/https/clientCertificate [8], advanced secret management, automated token rotation). Our goal is to provide NetSuite developers and architects a comprehensive, authoritative reference on secure SuiteScript-based API authentication and token management, fully supported by documentation and expert sources.
Introduction and Background
NetSuite SuiteScript is a JavaScript-based scripting framework used to customize and extend Oracle NetSuite’s cloud ERP. It enables backend code (Suitelets, RESTlets, scheduled scripts) that can integrate with external services via HTTP(S) and other protocols. As businesses increasingly connect NetSuite to third-party APIs – for order syncing, payments, shipping, CRM, etc. – securely managing authentication credentials and tokens becomes critical. Inadequate protection leads to exposures: stolen API keys, hijacked service accounts, or fraudulent transactions. Industry data confirms the urgency: in 2025, 99% of organizations encountered API security problems [9], and 95% of API attacks originate from misuse of valid credentials [1]. For example, high-profile API breaches (NASA, Uber, LinkedIn, etc.) often stemmed from leaked keys or tokens [1] [2].
SuiteScript’s architecture has evolved to meet these challenges. Early customizations sometimes used insecure practices (e.g., hard-coding credentials in script files or custom records). Recognizing this, NetSuite introduced controlled secure fields and modules. A pivotal feature was Form.addCredentialField (SuiteScript 2.x, 2015.2) [3], allowing developers to capture passwords or tokens in Suitelet forms without exposing cleartext to scripts or logs. Later, the N/crypto and N/https modules (also introduced in 2.x) provided encryption and HTTP utilities. Most recently, NetSuite added API Secrets (Setup > Company > Preferences > API Secrets) in 2021.1 [4] – a vault for storing sensitive tokens and certificates. SuiteScript now supports referencing these secrets via APIs rather than embedding raw values.
This report has the following structure: After this introduction, we outline the key modules and mechanisms (credential fields, secure strings, secret keys, API Secrets). We then analyze authentication patterns (API keys, OAuth, JWT, etc.) and how SuiteScript supports each. Next we present best practice workflows – e.g. storing secrets in protected fields, using createSecureString for HTTP headers, and managing token lifecycles. We include case studies of typical NetSuite integrations (e-commerce, cloud services, etc.) illustrating real-world implementations. Throughout, we incorporate data and expert guidance to frame security implications. Finally, we discuss future directions (like mTLS, improved key rotation), then conclude with recommendations.
Historical Context: SuiteScript 1.0 (pre-2015) had very limited support for secure storage – developers often encrypted data manually or avoided storing secrets altogether, placing trust in external scaffolding or user memory. With SuiteScript 2.x (2015 onward), NetSuite introduced the modular API model (e.g. N/ui/serverWidget, N/crypto, N/https), enabling more sophisticated key management. The credential field concept – introduced around 2015 – was a first step to isolate cleartext tokens. By 2021, data breaches and strong regulatory pressures prompted NetSuite to formalize secret storage – hence API Secrets. The landscape continues to evolve; recent updates (SuiteScript 2.1+) add certificate-based HTTPS, updated OAuth tooling, etc., reflecting the increasing complexity of enterprise API integrations.
SuiteScript Modules and Features for Credential Management
SuiteScript 2.x provides multiple modules dedicated to handling and securing credentials, secrets, and tokens. Table 1 summarizes the principal modules and their purpose:
| Module (Ns) | Key Features | Typical Use Cases | Supported Types |
|---|---|---|---|
| N/ui/serverWidget | form.addCredentialField(options) – adds a password/credential input to forms [3]. Credentials are stored encrypted on submission; scripts can retrieve only a GUID (not the value). | Capturing user-supplied API keys/ passwords in Suitelets or custom forms. E.g., a setup page for entering an OAuth client secret. Ensures credentials aren’t exposed in code or logs. | Suitelet (server) |
form.addSecretKeyField(options) – similar to credential field but specifically for keys; generates a GUID and encryption. (Introduced in SuiteScript 2.1 sample) [10]. | Creating forms where end-users supply passwords, keys or API tokens which are then encrypted and processed. | Suitelet (server) | |
| N/crypto | Cryptographic primitives: hashing (SHA1, SHA256, SHA512), HMAC (SHA256, SHA1, etc.), symmetric cipher (AES/CBC).Core methods: createHash(), createHmac(), createCipher()/createDecipher(), createSecretKey() [11] [12]. | - Generating OAuth1 signatures (HMAC-SHA256) or AWS SigV4. |
- Encrypting/decrypting data payloads or credentials.
- Checking password fields against stored values (
crypto.checkPasswordField). - Creating symmetric keys:
crypto.createSecretKey({guid, encoding})returns acrypto.SecretKeyreferencing an encrypted key value [12]. | Server scripts | | N/encode | Encoding utilities: Base64 encoding/decoding, UTF-8, HEX, etc. Typically used alongside crypto. | Encoding credentials for HTTP (e.g. Base64 for Basic Auth). Converting strings for HMAC input. | Both (server/client) | | N/https | HTTP and HTTPS interactions. Key methods: HTTPget/post/put/delete. Also:https.createSecureString(options),https.createSecretKey(options). The SecureString is a way to encapsulate sensitive fragments for safe transmission [13]. | - Performing API calls to external services (REST, SOAP) with secure headers or body. - Handling OAuth token endpoints (via HTTP).
createSecureString({ input: '{guid}' })wraps a credential GUID or API secret into aSecureStringthat can only be decrypted by NetSuite server [14].https.createSecretKey({ guid: '...', encoding })derives a key object from a credential field GUID [15]. Useful for e.g. HMAC signing. | Both (server/client; client supports limited features) | | N/sftp | Secure FTP client. Can use NetSuite-stored SFTP credentials for host/user/password. | Automating file transfers (invoices, data) to third-party SFTP; credentials stored in NetSuite and passed securely [16]. Can reference credentials via domain restriction. | Server scripts | | N/https/clientCertificate | (SuiteScript 2.1+) Supports sending HTTPS requests with client-side X.509 certificates. | Integrations requiring Mutual TLS (e.g. banking APIs, government). A SuiteScript 2.1 module to attach digital certificates to HTTP requests. | Server scripts (SuiteScript 2.1+) | | N/certificateControl | Manage NetSuite-stored certificates (Setup > Company > Certificates). Create, retrieve certs. | Handling certificate data in SuiteScript, possibly for custom encryption. | Server scripts |
Table 1: Key SuiteScript Modules for Secure Credentials and Authentication. Sources: Oracle Help Center, SuiteScript documentation [3] [15] [11]; community blogs [17].
When capturing or using credentials, these modules work in concert. For example, a Suitelet form can include a Credential Field; on form submission, the SuiteScript receives a GUID for that credential, not the plaintext. The script then calls https.createSecretKey({ guid: submittedGuid }) to obtain a crypto.SecretKey handle [15]. This key, securely held in NetSuite, can be used with N/crypto (e.g. HMAC or symmetric encryption). Alternatively, for simple transmission in an HTTPS call, the script could call https.createSecureString({ input: '{GUID}' }) (or '{custsecretID}' for API Secrets) to get a https.SecureString to set as an HTTP header or body [14] [6]. Notably, SecureString objects never expose the value in logs or responses – an empty placeholder appears if logged [18]. Thus NetSuite’s design ensures that sensitive tokens are kept encrypted at rest and in-flight.
Credential Fields and Form Fields
NetSuite’s UI module allows developers to build forms that accept sensitive inputs securely. The form.addCredentialField(options) method “adds a text field that lets you store credentials in NetSuite…for use when invoking third-party services” [19]. Crucially, “credentials associated with this field are stored in encrypted form” and “SuiteScript does not hold a credential in clear text mode” [3]. The field yields a GUID when submitted. A typical sequence is: A user opens a Suitelet form, enters a password or API key into the credential field, and the SuiteScript receives a GUID like 8ABE039DC0DF4453156805CDD18D1E26. That GUID can then only be decrypted by calling https.createSecureString({ input: '{GUID}' }) in a server script that has permission (often via restrictToScriptIds) [20].
An example from NetSuite’s sample scripts illustrates using a Secret Key Field (a variant of credential field) together with crypto.createSecretKey [10]. In the sample Suitelet, a form is created with form.addSecretKeyField(...), restricted to the current script ID [21]. On submission, the script obtains the submitted GUID, then creates a symmetric key handle via:
let sKey = crypto.createSecretKey({
guid: myGuid,
encoding: encode.Encoding.UTF_8
});
The script can then use sKey for HMAC or cipher operations [10]. This pattern ensures the raw credential (“secret key”) never appears in code or logs.
SecureString and SecretKey Objects
SuiteScript’s N/https and N/crypto modules introduce mechanisms for handling data as SecureString or SecretKey objects. A SecureString encapsulates sensitive data that can be safely included in an outgoing HTTPS request (headers or body) [13]. It can be created from either a GUID (from a credential field) or the script ID of an API Secret [5]. For example:
// Example: using API secret for Bearer token
let header = https.createSecureString({
input: 'Bearer {custsecret_api_token}'
});
Here, {custsecret_api_token} refers to the script ID of a secret in NetSuite’s API Secrets. The SecureString ensures the token is transmitted securely** [5]**. The Hood River blog shows a similar use in constructing a Basic Auth header by base64-encoding a {username}:{password} pair into a SecureString [22] [23].
A SecretKey (in N/crypto) is a handle to a cryptographic key without exposing it in script memory [24]. It is created via crypto.createSecretKey(options), passing either guid or secret (API secret ID) [12]. This key can then be used in cipher or HMAC operations. Notably, the encoding parameter ensures correct interpretation (e.g. AES requires 16/24/32 char keys [12]). The SuiteScript docs emphasize: “The handler does not store the key value. It points to the key stored within the NetSuite system. The GUID or secret is also required to find the key.” [25] This separation of handle from value is a security design; the script cannot inspect the key’s plaintext, only use it for cryptographic operations.
API Secrets (Secret Manager)
Introduced in 2021.1, NetSuite API Secrets are secure containers for tokens, passwords, certificates, etc., managed in the UI (Setup > Company > Preferences > API Secrets). As Oracle’s documentation states: “API secrets include hashes, passwords, keys, and other secrets for managing digital authentication credentials” and can be “referenced [in scripts], preventing the need for plaintext secrets in scripts” [26]. Once a secret record is created (with a name and script ID like custsecret_myKey), SuiteScript code can reference it in https.createSecretKey or https.createSecureString calls.
For example, using an API Secret:
let secretKey = https.createSecretKey({
secret: 'custsecret_my_api_app_key'
});
This returns a crypto.SecretKey for the value stored as that secret [4]. Likewise, https.createSecureString({ input: '{custsecret_my_api_app_key}' }) wraps the secret value for HTTP use [5]. Crucially, API Secrets bring strong access controls: a secret can be restricted to certain scripts, roles, or domains [27]. By default, values of secrets cannot be read directly by script; they’re only revealed through secure methods.
Benefits: An official blog notes that API Secrets “offer a secure and easy to use method to protect credentials,” enforce least-privilege, and solve issues of distribution in SuiteApps [28] [29]. For multi-tenant SuiteApps, setting the “Available to SuiteApp” option allows safe sharing of secrets to all customers of the app [30]. The API Secrets infrastructure also accepts very long values (up to a million characters [26]), accommodating anything from certificates to large keys.
APIs and Modules Using API Secrets: Both N/https and N/crypto can pull from API Secrets. As seen in the documentation:
https.createSecretKey({ secret: 'custsecret_...' })(since 2021.1) [4].crypto.createSecretKey({ secret: 'custsecret_...' })(since 2021.1) [31]. These let developers avoid exposing sensitive constants; instead they refer to the managed secret.
Secure API Authentication Patterns
SuiteScript integrations use a variety of authentication schemes depending on the third-party API. We analyze common patterns and demonstrate how to implement each securely with SuiteScript modules.
Basic Authentication (Username:Password)
Many legacy APIs still use HTTP Basic Auth, sending a header Authorization: Basic {base64(username:password)}. In SuiteScript, one should never hard-code such credentials. Instead, store the username and password in credential fields or API Secrets, and generate the header at runtime.
For example, suppose custsecret_api_user and custsecret_api_pass store the two values. Using N/encode and N/https, you can build the header as a SecureString [22] [23]:
// Create secure strings for user and pass
let secUser = https.createSecureString({ input: `{custsecret_api_user}` });
let secPass = https.createSecureString({ input: `{custsecret_api_pass}` });
// Append them with ':' delimiter
secUser.appendString({ string: ':' });
secUser.appendSecureString({ secureString: secPass, keepEncoding: true });
// Base64 encode
let secBase64 = secUser.convertEncoding({
toEncoding: encode.Encoding.BASE_64,
fromEncoding: encode.Encoding.UTF_8
});
// Build final header: "Basic " + base64 credentials
let authHeader = https.createSecureString({ input: 'Basic ' });
authHeader.appendSecureString({ secureString: secBase64, keepEncoding: true });
Then use authHeader in the HTTPS request:
const response = https.get({
url: 'https://api.example.com/data',
headers: { Authorization: authHeader }
});
At all times, the actual credentials never appear as plain strings in code or logs. The SecureString methods appendSecureString and convertEncoding ensure a runnable header is constructed without ever storing the plaintext combination [22] [23].
Bearer Tokens / API Keys
Another common scheme is Bearer tokens (e.g. OAuth2 access tokens, JWTs) or simple API keys sent as header or query param. These secrets should similarly be stored in API Secrets or a credential field. Using https.createSecureString simplifies handling. For instance:
-
API Key as Query:
let apiKey = https.createSecureString({ input: '{custsecret_api_key}' }); let client = https.get({ url: 'https://api.service.com/resource?key=' + apiKey });NetSuite will substitute the secure value of the secret at call time. Domain restrictions on the secret ensure it’s only sent to allowed hostnames.
-
Bearer Token in Header:
If you have a token that periodically refreshes, store the client ID/secret and perform the OAuth handshake in SuiteScript, then set:let bearer = https.createSecureString({ input: `Bearer {custsecret_token}` }); https.get({ url: 'https://api.service.com/userinfo', headers: { Authorization: bearer } });This is exactly how the Hood River blog examples illustrate Bearer usage [6].
OAuth 1.0a (Consumer Key/Secret)
Although OAuth2 is more common today, some APIs still use OAuth1.0a with signatures (Twitter, older services). OAuth1 requires generating a signature via HMAC-SHA1 or SHA256. SuiteScript can implement this using crypto.createHmac. For example, here is the flow for a signed GET:
- Collect necessary parameters (consumer key, nonce, timestamp, etc.), all of which can be stored as secrets or fields.
- Create a base string and composite key. The composite key
consumerSecret&tokenSecretis created from your credentials. - Use
crypto.createHmac({algorithm: 'SHA256', key: secretKey}), wheresecretKeyis acrypto.SecretKeyobtained viacrypto.createSecretKey({guid: guidOfSecret})[10]. - Update HMAC with the base string, digest to hex or base64.
- Construct Authorization header with signature.
The blog [33] notes this use conceptually: by utilizing N/crypto and N/encode within SuiteScript, “developers can avoid the need for external JavaScript libraries, such as CryptoJS.js, for signature generation” [32]. The excerpt elaborates that API Secrets (with strict access) reduce vulnerability compared to custom-record-based storage, and direct HMAC support makes implementations easier and more secure. A pseudocode snippet:
// Example: OAuth1 signature using HMAC-SHA256
let key1 = 'custsecret_otoken'; // script ID for OAuth token secret
let key2 = 'custsecret_okey'; // secret for OAuth consumer secret
let hmacKey = crypto.createSecretKey({ secret: key2 }); // using API secret
let hmac = crypto.createHmac({ algorithm: 'SHA256', key: hmacKey });
hmac.update({ input: baseString, inputEncoding: encode.Encoding.UTF_8 });
let signature = hmac.digest({ outputEncoding: encode.Encoding.BASE_64 });
This avoids exposing the secrets themselves; the digest can then be placed in an OAuth header or parameter.
OAuth 2.0 and Token Flows
OAuth2 (client_credentials, authorization_code, etc.) is widely used. SuiteScript can implement OAuth2 flows by making HTTP calls to token endpoints and storing the resulting access/refresh tokens securely. Best practice is:
- Store the client ID and client secret in API Secrets or credential fields.
- Store any refresh tokens or long-lived tokens in protected storage (custom encrypted field, not in script).
- On each need for access, check if the token is expired; if so, call the token endpoint via
https.post, using secure headers as above. - Example:
Then storelet clientId = https.createSecureString({ input: '{custsecret_clientid}' }); let clientSecret = https.createSecureString({ input: '{custsecret_clientsecret}' }); // Build Basic auth header for token endpoint let header = https.createSecureString({ input: 'Basic ' }); header.appendString({ string: Buffer.from(clientId + ':' + clientSecret).toString('base64') }); let tokenResp = https.post({ url: 'https://oauth.provider.com/token', headers: { Authorization: header }, body: { grant_type: 'client_credentials' } }); let accessToken = tokenResp.body; // typically JSON parsedaccessTokenin a SuiteScript context (or better, in an encrypted custom record field or cache) for later use.
NetSuite’s HTTPS methods will ensure the Basic header is sent only over TLS. Developers should secure refresh tokens similarly. There’s no built-in refresh in SuiteScript, so one may either run scheduled scripts to renew tokens, or use Suitelets that are triggered on-demand. Restricting which scripts can access the stored tokens (via script/role here) is important, echoing least privilege [29] [33].
Certificate-Based (Mutual TLS)
Increasingly, APIs demand mutual TLS (client certificates). SuiteScript 2.1 introduced the N/https/clientCertificate module. This allows sending an HTTPS request with a digital certificate loaded from NetSuite’s Certificate store [8]. Briefly, the steps are:
-
Upload a certificate/private key pair in NetSuite (Setup > Certificates).
-
In SuiteScript 2.1, use
https.requestwith an options object that includesclientCertificateandclientKeyvalues, referencing the stored certificate record. Example (from Oracle docs):const clientCert = certificateControl.loadCertificate({ id: 1234 }); // id of certificate record from NetSuite UI https.request({ method: 'POST', url: 'https://secure.api.com/data', certificate: clientCert, body: {...} });This module ensures that sensitive certificate materials are handled by NetSuite’s secure store, not hard-coded. A NetSuite professional article notes
N/https/clientCertificateis “designed to facilitate secure communications with high-security third-party systems” [34].
Token Refresh and Storage
Token management goes beyond initial auth. Access tokens usually have lifetimes (e.g. 3600s) and require refresh tokens to get new ones. SuiteScript provides no automatic token management, so scripts must implement this. A typical pattern:
- Store
refresh_tokenin a securely protected custom record or field (possibly encrypted withN/crypto). - On each execution of a script needing the API, check if the current
access_tokenis valid (or attempt API call and catch 401). - If expired, make a token refresh call via
https.post(as above) using the refresh token, update both tokens in storage. - If unable to refresh (e.g. long inactivity), fall back to browser-based OAuth flow (if interactive) or notify admins.
Throughout, ensure the refresh token is also wrapped in a SecureString or decrypted by a restricted process. One could use the API Secrets feature to store a refresh token (set to expire far in the future), and then reference it as {custsecret_refresh} in script just like any secret [5], though UI limitations (max secret length) may apply.
Session Tokens: Some services issue ephemeral session tokens; store these similarly in script parameters or records. If in a Suitelet form, could use a credential field to hold them transiently (though maybe not needed).
Best Practices and Data-Driven Insights
Adhering to security best practices is crucial. The following are supported by both industry data and Oracle recommendations:
- No Hard-Coding of Secrets: Embedding keys in code (even in SuiteBundles) is perilous. Obrador (atsourcepro) warns that hard-coded API keys risk exposure if code leaks [35]. Instead, use encrypted fields and API Secrets. The 2023 Oracle blog explicitly advises marking credential files as locked/hidden when packaging SuiteApps [36].
- Encryption At Rest: Any stored credential should be encrypted in the database. By using Suitelet credential fields or the API Secrets vault, NetSuite ensures encryption with its own key management [3] [26]. Avoid storing raw text (even in custom records) unless encrypted by code (
crypto.Cipher). - Encrypted in Transit: Credentials must only be sent to external services over TLS 1.2+ or SFTP (as docs note) [3]. NetSuite will enforce TLS for
N/httpscalls, but developers should avoid trivial "http" endpoints. - Logging Discipline: NetSuite will never log plaintext credentials (session notes, debug logs). Nevertheless, developers must not inadvertently log SecureStrings. For example,
log.debug({title:'cred', details: secureString})will output{}[18]. If you need to log non-sensitive data, decode carefully, but do not log secrets. - Restrict Scope: Use domain restrictions on credential fields to limit which hostnames can receive the secrets [3]. Also, use
restrictToScriptIdsor role-based restrictions to confine decryption access. The Oracle blog emphasizes least privilege on secrets [29]. For example, a Suitelet that obtains a token may be the only script allowed to decrypt it. - Rotate Regularly: Establish a process to rotate API credentials periodically. Many compliance regimes (e.g. PCI-DSS) recommend frequent key rotation. With API Secrets, set expiration or warnings in the UI [37].
- Audit and Monitor: Use NetSuite’s System Notes and scripting logs (without sensitive data) to track when credentials are accessed or changed. Monitor failed login attempts on external APIs. The Cloudflare report suggests that high error rates (e.g. 429 Too Many Requests) often indicate security misconfiguration [38]; watch for those signals in integrations.
- Secure APIs in NetSuite: File Cabinet and RESTlets themselves should be protected (Token-Based Auth for SuiteCommerce, etc.) separate from external API concerns.
Data Context: Our security imperative is underscored by data. According to Cloudflare’s 2024 report, nearly 60% of organizations permit write access to at least half of their APIs [2] – meaning that most companies allow potentially sensitive operations via APIs. In such an environment, any leaked credential can cause massive damage. On average, an API-related breach costs over $591K, with $832K in financial services [1]. Given that DreamFactory reports 99% of firms have had API issues [9], it is almost inevitable that an improperly handled NetSuite integration could be attacked. Notably, 95% of API attacks use valid credentials or tokens [1] – precisely the scenario our secure credential management is designed to prevent or mitigate.
Case Studies: Real-World Examples
To illustrate these principles, we present three representative integration scenarios. Each demonstrates how a NetSuite developer might use SuiteScript’s credential features.
Case Study 1: E-commerce (Shopify) Integration
A retail company syncs orders between NetSuite and Shopify. The Shopify API uses OAuth2 (with API keys and tokens). The integration uses a Suitelet as an on-demand connector:
- Credentials: The developer creates two API Secrets:
custsecret_shopify_key(Shopify API key) andcustsecret_shopify_secret. In the Suitelet, these are accessed viahttps.createSecretKey({ secret: 'custsecret_shopify_secret' })when needed for signature, and viahttps.createSecureString({ input: '{custsecret_shopify_key}' })when building URLs. - OAuth Flow: A one-time OAuth handshake is performed. The redirect from Shopify triggers a Suitelet callback, which captures the temporary code. The Suitelet then uses
cryptoto HMAC sign the request (Shopify uses Basic Auth on POST /token) using the secret. The response contains an access token which is stored in a custom encrypted field on the integration config record (not visible to users). Netsuite ensures at rest encryption. - API Calls: For subsequent calls, the SuiteScript constructs a header
Authorization: Bearer <token>usinghttps.createSecureStringas above. The domain (api.shopify.com) is whitelisted on the credential’s restrictions, preventing misuse elsewhere. - Rotation: The company sets a calendar reminder to regenerate API keys annually, updating the API Secrets through the UI.
This scenario highlights API Secrets and SecureStrings. Reference [31] describes a similar approach for building authenticated calls, emphasizing no cleartext in code [39]. It shows migrating from custom records to official secrets as “a small step that can make a significant security difference” [40].
Case Study 2: Payment Gateway (Authorize.Net) Integration
A payment processing Suitelet sends transactions to Authorize.Net, which requires a merchantLoginId and a transactionKey. These are analogous to username and API key.
- Credential Capture: The Suitelet form (for admin use) includes two credential fields: login ID and transact key. On submission, the script receives GUIDs. It then calls
https.createSecretKeyon each (as shown in the “SecretKey example” script) to get key objects. - Creating Signature: Authorize.Net HMAC-signs requests (MD5 hashing) with the transactionKey. Using N/crypto, the script computes the MD5 or SHA256 HMAC of the payload with
crypto.createHashorcrypto.createHmacusing the secret key object. This emulates Authorize.Net’s signature process securely. - API Calls: The payment data is sent via
https.post, including the signature. All sensitive fields go in the encrypted request body (SuiteScript ensures TLS). Nothing is ever logged or stored in plaintext. - Token Support: If Authorize.Net used a session token workflow (it can), the script would store tokens similarly in a protected record.
This case underscores Form.addCredentialField (admin-entered secrets) and N/crypto HMAC usage. If the old practice had been to place keys in script files, logs could accidentally expose them – which we avoid.
Case Study 3: Multi-Cloud Data Transfer
A client exports data files from NetSuite to AWS S3 nightly. The integration uses a scheduled SuiteScript with per-account AWS IAM credentials stored in NetSuite.
- Credential Storage: Using the SuiteScript AWS library (GitHub gist) or custom code, the AWS Access Key ID and Secret must be supplied. The developer opts to use NetSuite’s credential fields on a custom “Cloud Integration” record for each customer account. The fields are encrypted and limited to scripts with specific IDs (even if code is shared among accounts) [20].
- Request Signing: The script loads these via
https.createSecureStringto get plain values temporarily, then usescrypto.createHashoperations to sign S3 requests (SigV4). Acrypto.SecretKeyobject is derived from the AWS Secret Access Key GUID to HMAC the canonical request. - File Transfer: The script then calls the built-in
N/httpsor a built-in AWS SDK module to upload. For S3, NetSuite also hasN/sftpbut S3 needs HTTPS REST. - Security: The use of
restrictToScriptIdson the credential fields means only this scheduled script can decode the key in memory, reducing risk [20].
This illustrates high-volume, automated use of credentials. It also shows alternative means (some developers might use N/https.createSecureString with business logic to import certain libraries).
Security Note: In this case, ensure temporary keys have limited IAM permissions (least privilege) and rotate keys periodically. Although beyond SuiteScript, it is crucial that the IAM keys used by NetSuite scripts have only needed S3 rights, not blanket account access.
Implications, Challenges, and Future Directions
The above reviews and examples underscore several implications:
- Enhanced Security Posture: By properly using credential fields, SecureStrings, and API Secrets, an organization significantly reduces the attack surface. Data is encrypted at all stages. Oracle documentation asserts that adopting API Secrets aligns with “principle of least privilege” and improves account security [28].
- Development Discipline: These security features introduce complexity. Developers must understand the flow: storing a secret not as a value but as a reference, decrypting only when needed, and avoiding mistakes like accidentally logging a
SecureString. Training is required. However, the community indicates this discipline is well worth the risk reduction [36]. - Governance: Administrators can now control which scripts or roles can use which secrets [41]. This model supports enterprise governance. The SuiteApp blog recommends not creating a secret in the same target account to avoid duplication – instead deploy via a SuiteApp to share securely [42].
- Performance: Handling encryption in scripts has minimal overhead compared to the security benefit. While calling
cryptofunctions orhttpsmultiple times adds some latency, in practice API calls are dominated by network time. Using asynchronous (.promise) methods can also improve performance in batch scripts.
Known Limitations:
SecureStringcannot be manipulated like normal strings. For instance, you cannot easily insert substrings without special methods. But the provided API (appendString,appendSecureString, etc.) covers the common needs [43].- Mistakes in quoting GUIDs: Note that
https.createSecureStringexpects input patterns like'{GUID}'(with curly braces) [14]. Omitting braces or wrong syntax leads to errors. Developers should consult docs. - Visibility: Even if a script is running server-side, it cannot reveal the plain secret; thus additional logging/troubleshooting can be harder. However, this is a design choice for safety.
Future Directions: SuiteScript continues evolving. The introduction of the N/https/clientCertificate module [8] signals growing support for certificate and mutual-TLS workflows. Future enhancements might include built-in OAuth2 flows, managed token caches, or integration with external identity providers. On the broader industry side, the 2025 DreamFactory report (published Jan 2026) emphasizes API security automation and built-in controls [44] – NetSuite’s secure modules align with this trend.
Web API trends suggest:
- Zero Trust and IAM: Enterprises will likely move toward automatic key rotation and stronger IAM. SuiteScript roles/permissions already enforce part of this. NetSuite might add features like one-time secrets or integration with external vaults.
- Governance: As regulators and standards (ISO27001, GDPR, etc.) emphasize data protection, having clickable logs that cryptography was used becomes important (for audits). NetSuite’s approach gives evidence that plaintext was never stored.
- AI and Security: Emerging AI tools may help identify potential security misconfigurations in scripts. For now, developers must rely on code reviews and documentation.
Conclusion
Effective API authentication and token management in NetSuite SuiteScript require leveraging the platform’s secure modules and patterns intentionally and systematically. This report has provided an in-depth examination of SuiteScript features – credential and secret fields, SecureString, SecretKey, N/crypto, N/https, and API Secrets – that together deliver strong security. We have shown how to apply them in common auth scenarios (Basic, OAuth, HMAC, mTLS) and integrated best practices backed by authoritative sources and data.
Every sensitive credential or token must transit through NetSuite’s guarded infrastructure: captured via a credential field or API Secret, encapsulated in a SecureString, and exchanged over TLS. Oracle documentation and experts alike stress “never hold a credential in clear text” [3] [36]. By following these guidelines, businesses can protect against the overwhelming majority of API attacks (since ~95% exploit stolen credentials [1]).
Looking forward, SuiteScript will adapt as API security matures. Current innovation (like client certificates, expanded OAuth support) will be joined by further management features. Yet the core principle remains: external integrations are only as secure as their weakest credential handling. We encourage NetSuite architects and developers to review their code for any plaintext secrets, adopt the secure modules reviewed here, and establish policies (rotation schedules, least-privilege ACLs) that solidify NetSuite APIs as robust and resilient. With such diligence, organizations can harness powerful integrations without sacrificing security or compliance.
References: This report is grounded in NetSuite documentation [3] [15] [5] [26], Oracle developer blogs [28] [29], expert community posts [45] [35], and industry analyses [1] [2]. All technical claims and data points above are supported by these credible sources.
External Sources
About Houseblend
HouseBlend.io is a specialist NetSuite™ consultancy built for organizations that want ERP and integration projects to accelerate growth—not slow it down. Founded in Montréal in 2019, the firm has become a trusted partner for venture-backed scale-ups and global mid-market enterprises that rely on mission-critical data flows across commerce, finance and operations. HouseBlend’s mandate is simple: blend proven business process design with deep technical execution so that clients unlock the full potential of NetSuite while maintaining the agility that first made them successful.
Much of that momentum comes from founder and Managing Partner Nicolas Bean, a former Olympic-level athlete and 15-year NetSuite veteran. Bean holds a bachelor’s degree in Industrial Engineering from École Polytechnique de Montréal and is triple-certified as a NetSuite ERP Consultant, Administrator and SuiteAnalytics User. His résumé includes four end-to-end corporate turnarounds—two of them M&A exits—giving him a rare ability to translate boardroom strategy into line-of-business realities. Clients frequently cite his direct, “coach-style” leadership for keeping programs on time, on budget and firmly aligned to ROI.
End-to-end NetSuite delivery. HouseBlend’s core practice covers the full ERP life-cycle: readiness assessments, Solution Design Documents, agile implementation sprints, remediation of legacy customisations, data migration, user training and post-go-live hyper-care. Integration work is conducted by in-house developers certified on SuiteScript, SuiteTalk and RESTlets, ensuring that Shopify, Amazon, Salesforce, HubSpot and more than 100 other SaaS endpoints exchange data with NetSuite in real time. The goal is a single source of truth that collapses manual reconciliation and unlocks enterprise-wide analytics.
Managed Application Services (MAS). Once live, clients can outsource day-to-day NetSuite and Celigo® administration to HouseBlend’s MAS pod. The service delivers proactive monitoring, release-cycle regression testing, dashboard and report tuning, and 24 × 5 functional support—at a predictable monthly rate. By combining fractional architects with on-demand developers, MAS gives CFOs a scalable alternative to hiring an internal team, while guaranteeing that new NetSuite features (e.g., OAuth 2.0, AI-driven insights) are adopted securely and on schedule.
Vertical focus on digital-first brands. Although HouseBlend is platform-agnostic, the firm has carved out a reputation among e-commerce operators who run omnichannel storefronts on Shopify, BigCommerce or Amazon FBA. For these clients, the team frequently layers Celigo’s iPaaS connectors onto NetSuite to automate fulfilment, 3PL inventory sync and revenue recognition—removing the swivel-chair work that throttles scale. An in-house R&D group also publishes “blend recipes” via the company blog, sharing optimisation playbooks and KPIs that cut time-to-value for repeatable use-cases.
Methodology and culture. Projects follow a “many touch-points, zero surprises” cadence: weekly executive stand-ups, sprint demos every ten business days, and a living RAID log that keeps risk, assumptions, issues and dependencies transparent to all stakeholders. Internally, consultants pursue ongoing certification tracks and pair with senior architects in a deliberate mentorship model that sustains institutional knowledge. The result is a delivery organisation that can flex from tactical quick-wins to multi-year transformation roadmaps without compromising quality.
Why it matters. In a market where ERP initiatives have historically been synonymous with cost overruns, HouseBlend is reframing NetSuite as a growth asset. Whether preparing a VC-backed retailer for its next funding round or rationalising processes after acquisition, the firm delivers the technical depth, operational discipline and business empathy required to make complex integrations invisible—and powerful—for the people who depend on them every day.
DISCLAIMER
This document is provided for informational purposes only. No representations or warranties are made regarding the accuracy, completeness, or reliability of its contents. Any use of this information is at your own risk. Houseblend shall not be liable for any damages arising from the use of this document. This content may include material generated with assistance from artificial intelligence tools, which may contain errors or inaccuracies. Readers should verify critical information independently. All product names, trademarks, and registered trademarks mentioned are property of their respective owners and are used for identification purposes only. Use of these names does not imply endorsement. This document does not constitute professional or legal advice. For specific guidance related to your needs, please consult qualified professionals.